Targeted attacks via email takeover are currently the most common and successful form of cyberattack. Some 44% of firms have fallen victim to one.
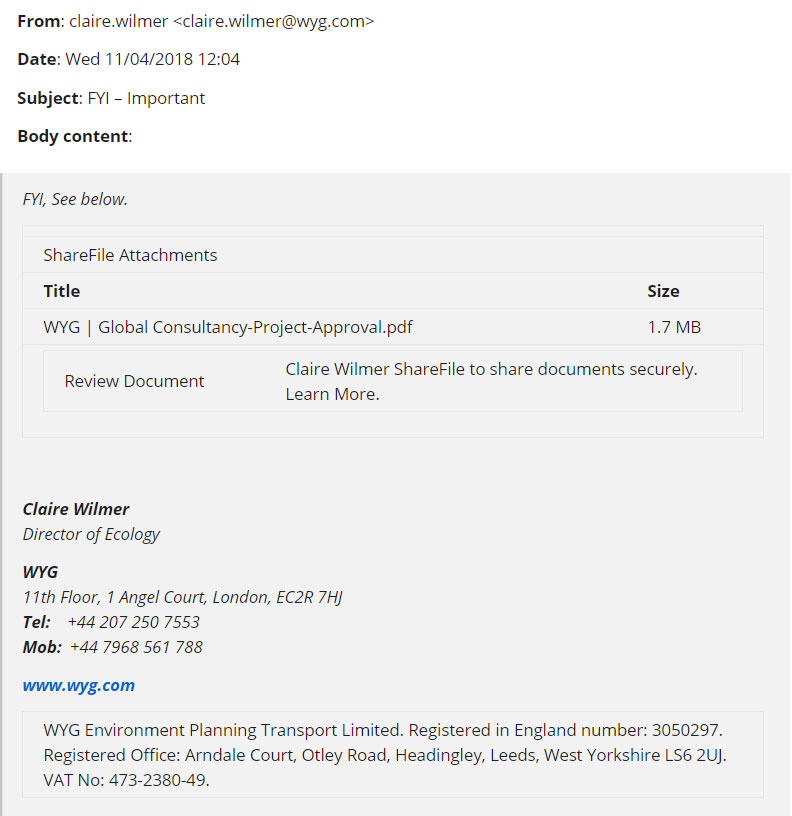
In May, Carmichael Consulting warned its clients of an aggressive, advanced phishing scam*, sometimes called the ShareFile scam or ShareFile virus, that was propagating across the Southeast. Attack victims received an email from a known associate telling them a file was ready for retrieval and asking them to provide their email address and log-in credentials to access it.
Those who fell for the ruse opened their address books and email stores to the attackers, which perpetuated the scam using the victim’s information. Attackers could harvest personally identifiable information (PII) from the victims, their co-workers and associates.
This group of threats, often called email account takeover or business email compromise attacks, are increasingly aggressive and deceptive. Spoofed messages and interfaces from an array of companies—Google Docs to DocuSign; Apple to Microsoft—have been leveraged to propagate email attacks.
In the most serious instances the attackers are nation-state actors from Russia, China and other countries, who are hired to seek access to corporate networks. Penetrating email accounts starts a chain of criminal activity like planting malware and delivering new messages that contain malicious links or requests for monetary transfers that appear legit.
How Can You Protect Yourself?
On the positive side, almost all these attacks can be thwarted with good security practices:
- Never provide your email address and log-in credentials—or any personal information—for any request you cannot verify. Although some email address requests are legitimate, reputable firms never ask for a user’s log-in password or other private credentials.
- Never click on a link in any email—whether it is to submit information or to download an “important” file—without confirming its source. Any text or box you are asked to click contains some form of link. Hovering over the object may show whether it is legitimate. Note that this is not the case with email sender names, thanks to account takeover mechanisms.
- For any suspicious or unexpected requests—whether to retrieve an unknown file or settle an overdue invoice, always confirm the request with the purported sender.
To request advice from Carmichael regarding any attack or suspected infection, or for any other service, please give us a call at (678) 719-9671.
*A phishing scam is one where an email message appears to be legitimate but clicking on some element of it will compromise the recipient’s PC, data, or other computing resources.

